Thibault Meunier: The importance of the Privacy Pass protocol
Presented by: João Tomé, Thibault Meunier
Originally aired on November 19, 2024 @ 5:30 AM - 6:30 AM EST
In this segment, João Tomé gets to know Thibault Meunier, a research engineer in Cloudflare’s research team. We cover his experiences in France and London and his interest in technology. We also discuss the importance of ending CAPTCHAs and the development of Privacy Pass, a privacy-preserving protocol aimed at eliminating CAPTCHAs. Additionally, we explore other applications for the protocol and other areas Thibault is working on.
Check the Cloudflare Research page: https://research.cloudflare.com
English
Research
Transcript (Beta)
Hello, everyone, and welcome to our Research Corner, the show where we get to know the people and projects of Cloudflare's research team.
I'm João Tomé, Data Editor and Storyteller.
I'm here with Thibault Meunier, a research engineer from our research team.
Bonjour Thibault, how are you? Hi João, how are you doing? I'm good, a little bit of a cold.
So we're going to discuss in this conversation about private paths and how it's used and the generally hated online captures, those little puzzles of sorts that one must do to enter a specific Internet site or service.
Actually, one must do in some cases and now less and less. But before we go there, something that is a work you have been doing, let's go back in time and learn more about you.
Where are you originally from? So I'm based out of France.
So I worked in London for Cloudflare for some time and moved back to the country, like following like the COVID pandemic.
In France, where are you originally?
Oh, I'm based next to Lyon. So basically it's like a city more or less like in the middle of France, which is like mostly known for like some food specialties.
So like if you like definitely like visit Lyon, like go and like eat cheese, like there's a lot of cheese, a lot of croissant, a lot of brioche, like really in terms of like pastries, like very good city if you want to visit.
Those are good. Those are good. How did you start being interested in technology?
First obvious, what was your background? And when you were starting becoming people like?
Yes. So I mean, I think like I started technology for like some time.
It's mostly and like that's pretty like very small. So I had like some time limit like on the computer and like had to go around just so like I could use a computer a bit more.
So it's very much like trial and error. I would say with like Cloudflare it's been similar when I was looking for like new opportunities, like I encountered like Cloudflare web pages quite often.
And that's like what pushed me to apply to Cloudflare, which is kind of like an interesting circumstance given the topic we're discussing today.
True. But when did you start really like engaging?
At what age? What was your first interest in terms of computing, in terms of technology?
So I started, I would say like 12, 13, something like that. Once again, I mentioned like first using just like dealing with a computer and then like started programming.
Interestingly, C for like random reason and do like various like algorithm programming for like competitive programming.
And then when I moved to college, went for a major in telecommunication and network, which is a bit remote from computer science, but not totally.
And moved back. Why were you interested initially on that specifically?
What drove you? Yeah. I mean, in terms of like the hobby, I don't know.
I just find it interesting. It was like various problems to solve.
I think the fact that you could have like a direct feedback and response is also very helpful.
I would say in a way, it's like I didn't have the opportunity to experiment with more like manual topics.
And so like computer was available.
It was kind of like a feedback response. Found something like interesting, like very set of like, should be like initially like a set of problems or like sort of like programs that you can do.
And that's it. And then you moved on also for to that more computing data science part, right?
Yeah. Then I did, which was like, I think, like more like more formal than like theory aspect.
And definitely was interesting and like still enjoy it today.
When did you start becoming like a proper researcher and trying to figure out things and solve problems and seeing, hey, I have a future in doing this type of research?
I feel that's like something which is like always like kind of like an ongoing question, because like you could always do a lot more.
There's like a lot of like interesting topics.
And I think I'm privileged to like work with a lot of like smart people, which are definitely like expert on a lot of like interesting topics.
When that happened, I feel it's more that like when I like started to look for a job, consider what I was able to do, seemed that that like, like being able to do like some programming was later like quite interesting.
And I think I went for that.
Like when I applied, that's something like I enjoy and like I still enjoy.
And that's it in terms of like being like a researcher, etc. I was never like much on like the academic side, I would say, of the research engineering panel, far more like on the engineering side.
And yeah, that's it. You actually, you went also as an intern to CERN in Geneva, right?
In Switzerland? Yes. Did that experience helped you in a sense in informing what you liked, what you wanted to develop to?
Yes, definitely interning us at CERN was like super interesting from like an engineering perspective.
So at CERN I was doing and working on like the infrastructure to allow like researchers to do their work.
So it was like more on the continuous integration pipeline, helping with like internal developer toolings, like dashboards and things and the kind of like own, I won't say property, but like there's a way like CERN works.
So for like those that don't know, CERN is like a laboratory in Switzerland, which like gathers a lot of like, it's like, like operates a large Hadron Collider and like, which help make like science discoveries.
And they manage like a lot of data, et cetera. And at least internal, like for me, was helpful to work at CERN in the engineering career to like understand like more what could it be even if it's like internal customers, definitely like discuss with them, engage.
That was, I think something very different that you, at least I didn't have before, should be like for competitive programming or for like discussing at university.
That was like something to feel like valuable, I think for me.
I've heard a lot of stories about CERN. It's one of the main physics and actually also astronomy laboratories of the world, quite known also because it was where the World Wide Web started back in the day.
But I've heard a lot of stories, especially on the different cultures that are there, although it's Switzerland, you'll get a contact as a researcher, as an intern with different cultures, different, actually different discipline, because there are people that do different things there, talk of their game.
Was that like an inspiration in some way too?
Definitely, like having the opportunity to discuss with like people of like different background, because like even for like internship, exactly as you mentioned, you have people that come from a bit all over the world.
You definitely have like a lot of like mentoring opportunities like in there.
And definitely that I think like widens kind of like what you could do with computing science.
I think that's one of the things like you mentioned initially, like what piqued your interest, I think is like I was interested, but that CERN, it kind of like expanded in terms of like what possible in terms of like the number of data, like the depth of the research that can be done on like very specific topics.
Also, like the engineering that you can have. And definitely like that, that piqued my interest.
I think of all the other thing, which is interesting, like the way I think CERN works is quite different from what you would have like in other companies or like even like what you would have at Cloudflare, because it's like really dedicated to research.
And definitely like this kind of like emulation that you can have is very nice.
The fact that people actually like come to CERN, so like most of the people are foreign and not necessarily like established, also bring like a bigger sense, I feel of like integration, because it's definitely like part of the culture that you would have.
Makes sense.
You joined Cloudflare in 2019, right? I do. When did you start really working on things like privacy pass and trying to end captures in a sense?
Was it right away?
How was that process in the beginning? Yes. So it was not right away. It was like I was like more, I think, like helping like some of the researchers like put the work out.
So like privacy pass, like I think started at Cloudflare much before I started, started in like 2017 with a release, so like two years prior I joined.
And like at least like on my side, like the help was more when they needed to have like new experiments and like some engineering work done like with JavaScript.
I think that's more where I helped. Where does that fit in like the Cloudflare story about like reducing the amount of capture?
I feel it's kind of like the second phase that Cloudflare had.
The first phase was really to like provide more accessibility to people and like reduce the number of like capture and challenges people encountered.
So that was the first phase and why privacy pass was launched in the first place.
Then a second phase came when Cloudflare was faced like with a choice to like move away like from Google reCAPTCHA product.
There's like a very nice blog, I think, on Cloudflare about the changes like Cloudflare made to move away from like reCAPTCHA to use hCAPTCHA and at the same time start an internal effort to actually like replace and like start the next phase which was called noCAPTCHA and that's like the second phase that like Cloudflare had to to launch like a product we call Turnstile and also like improve like the challenge part of like Cloudflare that handles challenges to reduce and like the number of like challenges and so like CAPTCHAs that people have and make Cloudflare CAPTCHA free.
You were mentioning Turnstile. This actually is a blog post from September of last year, so recent, but it was when we turned Turnstile free for everyone.
But before it wasn't free and since September 2023 it became free, that specific service, right?
Yes, it does. Definitely like I have like a high level understanding of like Turnstile and if you want to like deeply understanding, check out the blog.
It's like it's much more vetted than like what I could say. But the real idea here is that because Cloudflare like started to use it for like their own internal purposes, there was like a like bigger interest in terms of like integrating these same capabilities directly in like at the end of like a form for instance for submission or at the end of like email mailing list etc.
And that's how like the product came to be and like Cloudflare being committed to offer like as much capability to people and make the web a better place, like move forward and release CAPTCHA free for everyone.
Just for context, CAPTCHA specifically, it's an acronym, actually this is a Portuguese page, let me put it in English for our users.
But CAPTCHA means, in this case, it's a term that was coined actually more than 20 years ago in 2003 and it has a specific meaning in a sense, right?
Yes, it does.
So the idea is that it should be like it's a test which is automated and which should be able to tell if you're human or not.
And it has definitely had a lot of iteration.
So I think you could go like through the Wikipedia page and there's definitely a lot of research assessing the different types of CAPTCHAs.
The one people would be like the most familiar with nowadays is the one with like images and I think that's the one which kind of like made the trade off of like making accessibility to website a bit worse for certain people.
So like select buses or etc.
With the benefit of like making it harder for bots to go through. Initially, it was like simpler.
So I think that's exactly what the Wikipedia page showed.
There was like a test which was like some kind of like weirdly looking text and like letters that you had to type through.
Some of that at some point was also like with Google Books, for instance, that like took some text and like help you decipher this thing.
You could also have audio CAPTCHAs, you could have like mathematical CAPTCHAs, like how much is like one plus one, for instance.
The idea behind all these is really to make it harder for bots to go through with capabilities that we do think human processes or that legitimate traffic process.
In a way, you could say that like turnstile is also like a CAPTCHA thing because we want to tell human and bots apart.
It just has taken a very different take on like accessibility for this CAPTCHA.
And that's why we consider it a lot easier for users while preserving the same security.
Makes sense. You actually wrote this blog post in 2021 already that puts some numbers in terms of humans, the time that humans waste doing CAPTCHAs because it's a time-wasting process, that specific thing.
And 500 years that are wasted per day in terms of humans doing CAPTCHAs, it's quite a madness number.
So this was a process since 2021 that you've been working on.
How would you define the work specifically? So I think in 2021, so like the blog we published was about like trying out like a new method to give like an alternative to CAPTCHA.
And like definitely like I think that it's all, as you mentioned, like was a catchy one, was like 500 years lost, was like mostly based out of Cloudflare data at the time.
One of the things that it might not encompass is like also like the huge variance between users, because like certain users might see more CAPTCHAs and certain users might not.
And definitely that's why like we needed like more capability and more challenges to actually like go around that.
And this work I think was part of that, which uses the capability of that like at the time bots didn't have like much like YubiKeys or like Fido compatible devices.
And that made it a good competitor, I would say for challenges, like a good candidate to grow for these challenges.
It was the first attempt in a sense, right?
It was like one of the first attempt. And that's why when we released it as part of the challenge platform, we compared it and like gathered some data compared to like what will become Turnstile, because that was not out at the time, performed and how like other methods performed.
It's really to strive for experimentation, I think.
And that's what we're still trying to push forward. I didn't mention before, but CAPTCHAs, the term is related to completely automated public turning test to tell computers and humans apart.
It's a very long name, but also a very clear one.
You will understand what CAPTCHAs means by that name. But how did privacy pass?
You wrote a recent blog post in January about it, upgrading to the latest protocol version in this case.
How did privacy pass came about? So I think in this story, privacy pass was like a tool that was developed initially a bit outside and adopted and supported by Cloudflare to improve access for VPN and multiple users which are behind a shared IP.
So that means there's multiple computers behind a shared NAT or a single IP and really improve the way that they can browse Cloudflare websites.
And it turned out that that's also something that as part of a fostering commitment to privacy, which for instance, the launch of private relay, which essentially is also having multiple users behind a limited set of IPs.
The idea about privacy pass came back saying that we might be able to apply the same technique that we had for VPN users to private relay.
And that's really how privacy pass came into the story as a way to provide certain information in a privacy preserving manner.
In the case of private relay, for instance, iOS devices or macOS devices are attested by Apple as a legitimate device.
And this is a good sign that the user is legitimate.
It's definitely not the only tool that we have, but it's one tool that we factor in a decision.
The good thing about privacy pass is it's used for private relay to understand if Apple device is legitimate or not.
But it's a lot more broader. It's not a standard that has been pushed through ITF solely for Apple.
It's something more broad. And what the research team worked on is a way for anyone to deploy their own attestation.
So that if you come up with the same attestation we were discussing before with YubiKey, you can directly integrate with privacy pass.
If you come up with a new way to tell human and bots apart, you could still include it in privacy pass.
So people will not know exactly how the attestation is conducted for users, but they would know that they've passed your attestation.
And hopefully, down the line, it's sufficient to let people through and access website if some checks have to be performed.
Makes sense. You actually have a timeline here, a brief overview of the changes that, in this case, the protocols went over.
So this is one of the methods of trying to end CAPTCHA specifically, right?
In the larger scope of trying to get to that situation, what is still needed?
What are the steps that are being done by us and others to try to end this attestation process?
I don't think down the line, exactly like as you mentioned, for the definition of CAPTCHA, which is to tell humans and computers apart, it will still be an ongoing challenge because humans are in the real world, while computers live in a different infrastructure.
So that's like an ongoing process and we're trying to refine and make it the least painful for users.
So trying to find something which is easy for us and hard for computers.
It does not mean that with a lot of computers, et cetera, you could not pass it down the line, but that's something we're really focused on.
So I think you could follow the blog to listen on changes to Turnstile.
And also as part of the research team, we're really trying to foster the diversity of attestation that is possible to pass.
And that would give like a certain signal, not necessarily like something binary saying like, you're human or you're not, because it's really like a realm of probability, but something that would be better than like tossing a coin while being limited in user interactivity.
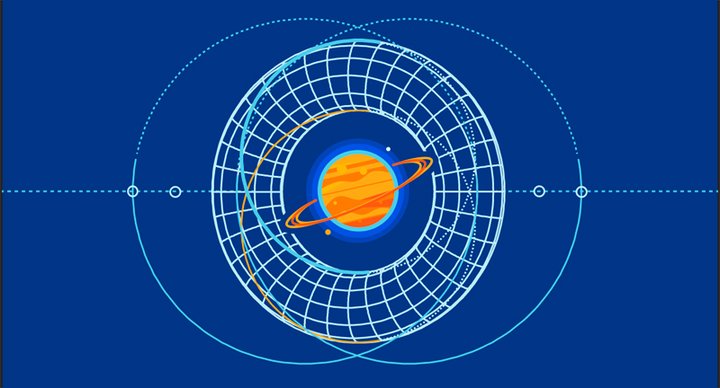
Actually, there's this illustration that shows this specific situation, right?
The request, the token that is asked. It's a communication trying to attest that you're human and you should be using the site, the service, right?
So I think the diagram that you're showing is to showcase how privacy pass when it's done interactively works.
And that's how it's used at the moment by Cloudflare. So what happens is Cloudflare to understand if you're human would return you a challenge, more or less a random number.
And we'll say, okay, if you return me a cryptographic signature of this random number by an external party, I'm okay to let you through.
And so what your device will do is it will work. So in this case with Apple to prove that it's a legitimate device and that's what Apple will require.
And once the legitimacy of the device has been tested, your phone will pass a random number to Apple, which will pass it to Cloudflare like a service, which is different from the service that challenged you.
And Cloudflare will sign this random number, pass it back to your phone.
And the phone will finally pass it back to the original website that challenged you and that requested you a signature.
And so all that happens in the background on your phone.
I described it at the higher level. There are multiple levels of cryptographic blinding.
So in the end, each party only see very limited information and no one is fully able to correlate the data.
And that's what makes privacy pass private.
It's private and it works in terms of authenticating the user as a human.
Even if in reality, like you were saying, in this case, it's the device that is being authenticated.
But there's this relation that this device is used by a user, a human user.
So I'm authenticating you as a human user in a sense.
In a sense, that's what happened. It's more that there's like a high correlation, at least in what we observed so far, that if your device is legitimate, then it's likely that you are legitimate traffic and we will let you through as a human.
Maybe down the line, this relation will be broken and it might happen that if you have a legitimate device, it doesn't give any information about if it's legitimate traffic or not legitimate traffic.
And that's why we keep on investing to research new solutions or alternative solutions to attest that fact.
We also have in the same blog post a demo in a sense related to what was done that is available on our research page, right?
What is this? So you can go on demo-pat .research.claflare.com and the idea of the demo is not everyone has access to an Apple device.
And even when you have access to an Apple device, it might be hard for you to understand what happens behind the scene.
And the idea of the demo is by installing an extension, which is called Silk, on your browser, you will be able to actually go step-by-step to understand how privacy pass works and make your browser actually perform a privacy pass authentication with a lot more detail.
This authentication, so Apple, for instance, checks that your device is legitimate.
What the extension would do is it will check that you're able to solve a turnstile challenge.
So it's kind of interesting that you have a loop around, you're legitimate if you pass a turnstile challenge, but this is really for research purposes and therefore we label it as a demo.
You can go through that on Chrome and Firefox.
We provide extension for both browsers. And if you don't want to go through, you also have screenshots on the blog.
And so you can just walk through by sliding on your phone, on your laptop.
Exactly. It shows, in a sense, the process that is being done, right?
Yes. And this extension is also configurable. So if you've down the line, you're a developer and you want to create a new type of attestation, you can add that to the extension.
We also provide some templates for you to start your own attestation method or start your own issuer, which are specific components in the privacy pass specification.
And this should help you get started with privacy pass and authenticate your user privately.
There's also some mention here exactly on how to use privacy pass today, try to adopt it in a sense.
Yes. And everything is like, at least the work that the research team did, is to make privacy pass as accessible to everyone.
And so all our code base is open source.
We try to provide documentation, keep all our library updated. And really, I think what, if I want people to understand one thing out of this podcast is Cloudflare uses privacy pass for CAPTCHAs because that's one of the important business we are in to keep our customers safe and keep users safe and have access to the web smooth.
At the same time, the privacy pass protocol is a lot more large than CAPTCHAs.
And if you want to use it only to pass a single bit of information to your website, that's something you can do.
And we don't know all the use cases that could be done with this protocol, but hopefully these tools foster like new research and help like researchers and developers to start working towards that direction.
The main objective in general is again for more use cases, more situations where CAPTCHAs, specific CAPTCHAs are not needed.
And this type of process can be used instead, right?
More quick. So yeah, it could definitely be for CAPTCHAs.
It could be for other things. For instance, one of the use case, you could have a privacy pass is you could decorrelate like the payment provider from like the account that did the payment.
So in this way, as a user, you could access a service and the provider of the service will know that you paid, but they would not know what method you've used or how you've used it.
It may not suit every application, but that's one of the things you could do.
It's definitely not related to CAPTCHAs, but that's something you can do.
And really, at least for CloudFlight, definitely if you want to like start your new attestation method to improve anti-fraud and have alternative to image-based CAPTCHAs, definitely come and talk to us.
However, if you also have use cases which are not CAPTCHA-based of privacy pass, you can come talk to us as well.
We'd be happy to provide support, even though it might not be immediately usable by CloudFlight.
Makes sense.
In a way, we're also adding to this basis, right? It works as a basis for future work, future endeavors.
That's the advantage, I think, in terms of protocols of building a protocol, then you can build up on that in a sense, right?
Yes.
In a way, we've also formulated that the protocol has been built because we had a few use cases and we've noticed a lot of use cases of privacy pass.
So there's been definitely some usage by CloudFlight for alternative CAPTCHAs.
There's been some usage by Brave, for instance, to understand how you could retrieve...
So Brave has this private ad system and how you could retrieve some of the reputation for that.
There's been some use cases with ZK apps, which is a way for people to access applications without exposing too much information about themselves.
And really, this diverse set of use cases of privacy passes kind of suggested that coming together, and that's where the IETF came through, to better standardize the protocol and have it as part of an Internet spec, definitely makes sense.
And again, the protocol and IETF, as you were mentioning, which is the that creates, puts in place the protocols, allows for others, different companies, actually new companies that come around, they'll use the same protocol.
So it'll be in the same standard, in a sense.
So everything will work on the Internet because of those protocols.
The idea is really to foster interoperability of this standard and build it in the open, in a way.
In terms of your work specifically on private pass and the work of the research team, what are the current and next steps that you'll see here, specifically?
Yes. So at least for the research team, and I'm not the only one working on that, so definitely want to thank all the people that work on it, and I'm only the voice for them.
But at least for work we're currently doing.
So as you mentioned, the blog in January, open source, the implementation integrated within Cloudflare existing ecosystem.
And really what we're looking for down the line is to experiment exactly with more diversity for attestation.
So hopefully down the line, we deliver new attestation, which are still private, and also improve some of the performance that we have.
The whole implementation that we have for privacy pass at the moment is purely in JavaScript because it was easier for us to build, easy to deploy.
We're looking to improve performance on that side.
Finally, another topic we're working on is privacy pass is an active area of research and an active area of protocol development.
And there are new types of way to...
new specifications which are being done for the protocol.
So should it be adding metadata, work with rate limiting, or have new type of signatures which might be more privacy preserving.
And that's something we keep on researching, evaluating if it makes sense for us, evaluating if the protocol is well-designed.
And that's something we're definitely now that we have the basis for the implementation, making it evolve so we can actually try out this new extension to the protocol.
And it seems that there's promise there, right?
In terms of different implementations, some may be more successful and more quickly implemented, others potentially more down the line, or there's always some experimentation, right?
In these types of protocols, where can they go in a sense?
Besides captures, do you think there's a promise of this protocol in other very specific cases you'll see more quickly being implemented?
I'm not sure exactly which one will come next, but definitely, for instance, having a way to do rate limiting in a privacy preserving manner is definitely interesting because that would not necessarily require a heavy state on the client side or more fingerprinting that could be done while still providing the benefit that you want of being able to rate limit your API or rate limit access to your network or something like that.
So I definitely do think that's promising. There's a lot of discussion, I think, on how to use metadata, but the topic is rather broad.
So that's definitely something that hopefully will be engaged down the line.
Yeah, it could be interesting to see what use cases come. What are the advantages of working on the research team on Cloudflare in relation to working on something and then seeing it implemented in real devices with real people?
Is what is the understanding in the company of the work that research team does and then how is it implemented?
So I think the advantages of the research team, and I would say that all team at Cloudflare are working on cutting edge problems and also the fact that Cloudflare has a widespread network, making it very compelling, at least as an engineer, for a lot of application.
It has a huge cache, it has all the worker platform, there's a compute and storage platform for a lot of people.
Operates like a large zero knowledge, like a VPN in the form of WAP. And all these teams, I know the research team, and they're doing super interesting problems.
I think the research team is more focused on what could come next after that.
It doesn't necessarily mean specifically with a product in mind, but definitely fostering what could be good for the Internet in terms of infrastructure.
So the team has launched a lot of product going in this direction in the past.
Should be for HTTPS for everyone, even though that's a bit old. But there's also the various certificate transparency monitors helping fostering post-quantum is also part of the team.
And the team is definitely uniquely placed to, at the same time, engage internally to understand what could be interesting areas to go through and also engage externally so that people that could leverage an edge network with the span of Cloudflare can actually work with them and foster new types of application.
And to that end, I do think that the success of Cloudflare privacy efforts should be with private relay, privacy password, et cetera, definitely encompasses good thing that the team has been able to enshrine.
Makes sense.
And you gave very specific and interesting examples of something that started in the research side.
It went all over the Internet, like HTTPS, and there's security in place there.
There's cryptography, there's making the Internet secure, but also that security being free, so available to everyone in place, which are good examples.
Any dreams that you have as a researcher of, hey, I really wanted to, in the next, I don't know, possible not the next year, but in the next few years, I really want to deal with this problem, try to solve this problem.
Is there something on your mind there specifically for the future?
I think that's a big question. But if we focus on what we can do with privacy pass, who has been the topic of this one, I feel that being able to understand how we could leverage privacy pass for a more open and transparent bot detection could definitely be interesting.
Maybe it's not with privacy pass, maybe it's with another type of protocol, but I have a strong belief that with the multiplication of, I would say, privacy proxies, I don't necessarily mean Cloudflare product, which are related to privacy, but should it be people starting to use some VPN, or protocols being deployed by clients to actually preserve the privacy of users, understand better where the data is.
I do think that bot mitigation would definitely be an important role in that, and understanding how this will all come together and find new ways to deal with this would definitely be interesting.
How it will look like, I don't know. I'm excited to see, and that's definitely an interesting area of research.
Absolutely, and it deals a lot with privacy, with security, with is it a bot or not, because sites need to know is this a bot or not to be safe, but also to be quick.
So there's a lot going on there, and it's really exciting to see that sometimes it comes from a very technical situation, and it has a real impact to users.
It captures a good example there, specifically.
I think I do agree, and I would not put it in terms of, is it a bot, not a bot?
I might have said that, I'm sorry for that in the past, but if it's a bot, not a bot, human or not human, I feel like what Cloudflare provides in terms of securing origins is not necessarily you will only have human on your website, or you will not have bots on your website.
It's more like allowing the traffic that people would like through their website, the traffic that is deemed legitimate, and that's definitely the question, which is very specific to each origin.
Each website may have a different definition of what's acceptable, not acceptable.
It might be bound to, is it likely human or likely a bot? It might be bound to certain location.
It might be bound to certain time of the day, because you're conducting maintenance, and I really feel that being able to somehow classify the traffic, understand what the origin wants, what's deemed legit, not legit, is kind of like a rabbit hole you can go through, and would require a different method for each of these topics.
Makes sense, and I think captures are a good representation of that, because there's a lot of technical details into from you doing those captures that are so annoying, to just clicking on a check box, and then you're in the site.
For the user, it's just, oh, this changed, oh, this is so easy now, just clicking, but there's a lot of technical details in the and they happen really fast compared to the time a capture takes.
They happen really fast, so it's quite interesting to see the steps that the Internet still is taking to become better, faster, reliable, private, too.
Yeah, I mean, definitely seeing the capture, the evolution that they had from no capture, because there was no traffic, to some text capture, to some image-based capture, to some more transparent capture, like Twinstyle is, is definitely an interesting ride.
Maybe down the line, maybe image capture might come back.
Who knows? It really depends on the evolution of capabilities from bots, what actually website capabilities that they do have to handle, and I mean, I do hope that I would not click on buses anymore, and that's what we're working on, the team is working on.
At the same time, there might be interesting solutions that pop out down the line, and will really depend on the deployment and the work that we would collectively do.
It does not solely rely on Cloudflare, and I do think on that side, even though we have an important role to play, we also need to discuss with people in the industry to come together to an acceptable solution on that side.
Makes sense, and it's quite an interesting topic to see it play out as it has.
Thank you so much, Thibaut. Any other thing that you think that the audience should know about the research team that they wouldn't probably know?
I think definitely you can go out to research.Cloudflare.com, which is a website we curate with the current set of active projects, the people that are working on it, as well as a curated feed for that.
And also, if you're thinking about an interesting problem that could be relevant and could benefit to the Internet, feel free to reach out to us on ask-research.Cloudflare.com or directly on our website.
We definitely welcome opportunities. We're hiring, and I think that's the case for the whole of Cloudflare.
You could either go to the career page, or if you are enrolled in an academic institution or are researching a specific topic, definitely feel free to reach out to us.
Sure. Here is the site for everyone to see.
Yes. Thanks, Raoul, for showing the website. There's both how Cloudflare is thinking about research, so a longer explanation than the one I gave, and definitely all the projects we're actively involved in, even though we're open to explore new areas.
For sure. Thank you so much, Thibaut. This was great. I learned a lot.
Thanks, Raoul. And that's a wrap.